Hello friends,
In this article, I will explain What is Cross-Site Scripting (XSS) attacks and
how to prevent -Site Scripting (XSS) attacks
What is Cross-Site Scripting (XSS) attacks
Cross-Site Scripting
(XSS) attacks are a type of injection, in which malicious scripts are injected
into otherwise benign and trusted websites.
XSS attacks occur when
an attacker uses a web application to send malicious code, generally in the
form of a browser-side script, to a different end user.
Flaws that allow these
attacks to succeed are quite widespread and occur anywhere a web application
uses input from a user within the output it generates without validating or
encoding it.
An attacker can use XSS
to send a malicious script to an unsuspecting user. The end user’s browser has
no way to know that the script should not be trusted, and will execute the
script. Because it thinks the script came from a trusted source, the malicious
script can access any cookies, session tokens, or other sensitive information
retained by the browser and used with that site.
How to Protect Yourself
The primary defenses against XSS are described
in the OWASP XSS Prevention Cheat Sheet.
Also, it’s crucial that you turn off HTTP TRACE
support on all web servers. An attacker can steal cookie data via Javascript
even when document.cookie is disabled or not supported by the client.
This attack is mounted when a user posts a
malicious script to a forum so when another user clicks the link, an
asynchronous HTTP Trace call is triggered which collects the user’s cookie
information from the server, and then sends it over to another malicious server
that collects the cookie information so the attacker can mount a session hijack
attack.
This is easily mitigated by removing support
for HTTP TRACE on all web servers.
How to
Prevent XSS -
To keep yourself safe from XSS, you must sanitize your input.
Your application code should never output data received as input directly to
the browser without checking it for malicious code.
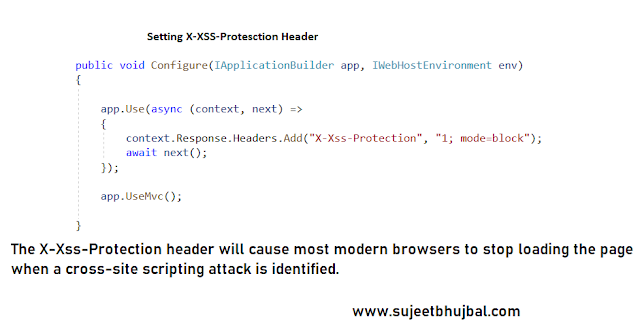
One of the steps in the process is to use the 𝐗-𝐗𝐒𝐒-𝐏𝐫𝐨𝐭𝐞𝐜𝐭𝐢𝐨𝐧.
X-XSS-Protection is a header that can be set on a
webpage to activate “limited” XSS protection in certain browsers.
1.
X-XSS-Protection: 1 : Force XSS protection (useful if XSS protection was disabled
by the user)
2.
X-XSS-Protection: 0 : Disable XSS protection
3. The
token mode=block will prevent browser (IE8+ and Webkit browsers) to
render pages (instead of sanitizing) if a potential XSS attack is detected.
Syntax:
𝐗-𝐗𝐒𝐒-𝐏𝐫𝐨𝐭𝐞𝐜𝐭𝐢𝐨𝐧: 1; 𝐦𝐨𝐝𝐞=𝐛𝐥𝐨𝐜𝐤
- This enables XSS filtering. Rather than
sanitizing the page, the browser will prevent rendering of the page if an
attack is detected.
Please Note: Some of the popular browsers
like chrome, edge have changed their policy of implementing XSS protection.
This means that if you do not need to support legacy browsers, it is
recommended that you use Content-Security-Policy without allowing unsafe-inline
scripts instead - we will talk about that in the next post.
Example:
Don’t forget to leave your feedback and comments below!
Regards
Sujeet Bhujbal
--------------------------------------------------------------------------------
Blog: www.sujeetbhujbal.com
Personal Website :-http://sujeetbhujbal.wordpress.com/
CodeProject:-http://www.codeproject.com/Members/Sujit-Bhujbal
CsharpCorner:-http://www.c-sharpcorner.com/Authors/sujit9923/sujit-bhujbal.aspx
Linkedin :-http://in.linkedin.com/in/sujitbhujbal
Twitter :-http://twitter.com/SujeetBhujbal
------------------------------------------------------------------------------